In the early days of containerization, we were focused on speed—shipping code faster and scaling effortlessly. However, as Kubernetes became the operating system of the cloud, it also became a primary target for sophisticated attacks. Security can no longer be a final “check-off” at the end of a sprint; it must be the very foundation upon which your cluster is built. The Certified Kubernetes Security Specialist (CKS) is the industry’s most rigorous performance-based exam. It doesn’t just ask you questions; it places you in a broken, vulnerable environment and asks you to fix it. Passing this demonstrates that you possess the hands-on skills to protect a production perimeter under real-world pressure.
Understanding the Kubernetes Certification Landscape
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Kubernetes Security | Expert | Security Engineers, Senior DevOps | CKA Certification | System Hardening, Network Policies, Runtime Security | 3rd (After KCNA & CKA) |
| Kubernetes Admin | Professional | SREs, Admin, DevOps | None | Cluster Architecture, Installation, Troubleshooting | 2nd (After KCNA) |
| Cloud Native | Associate | Students, Managers | None | Ecosystem overview, Terminology | 1st (Start here) |
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What it is
The CKS is a performance-based certification exam that tests your ability to secure container-based applications and Kubernetes platforms during the build, deployment, and runtime phases. It is designed to validate that a candidate has the technical proficiency to mitigate threats across the entire cloud-native lifecycle. Unlike multiple-choice exams, this requires solving complex security scenarios in a live command-line environment.
Who should take it
This certification is intended for experienced Kubernetes administrators who have already earned their CKA and are responsible for the security posture of their infrastructure. It is the ideal path for Senior DevOps Engineers, DevSecOps Specialists, and Cloud Architects who need to implement regulatory compliance and data protection. If your job involves protecting sensitive customer data within a cluster, this is your mandatory benchmark.
Skills you’ll gain
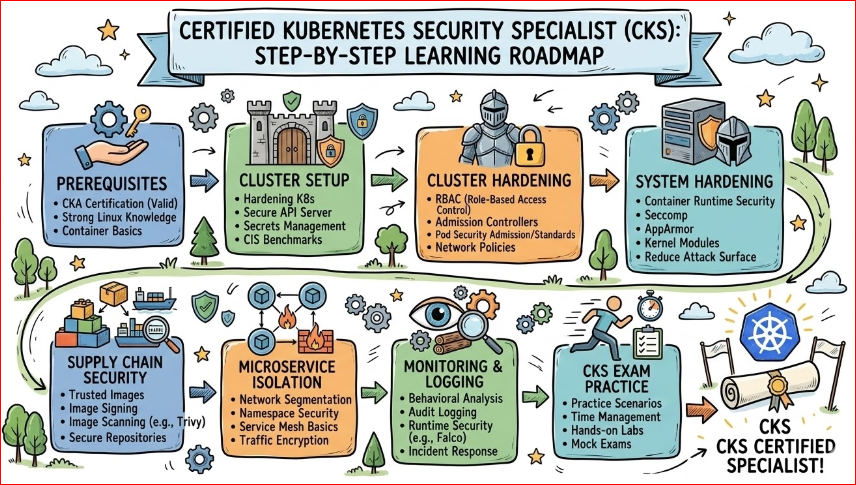
- Cluster Setup & Hardening: You will learn to secure the API server, Kubelet, and etcd by restricting access and using secure communication protocols.
- System Hardening: Mastering OS-level security modules like AppArmor and Seccomp to restrict what processes can do on the host node.
- Microservice Security: Learning to implement Pod Security Admissions and fine-grained Network Policies to ensure a “Zero Trust” internal environment.
- Supply Chain Security: Gaining the ability to perform image scanning, static analysis of manifests, and signing images to ensure only trusted code runs.
- Monitoring & Logging: Setting up advanced runtime security tools to detect behavioral anomalies and potential intrusions in real-time.
Real-world projects you’ll master
- Zero-Trust Networking: Designing a cluster where every pod is isolated by default, requiring explicit permission to communicate with any other service.
- Automated Vulnerability Pipelines: Building a CI/CD workflow that automatically blocks any container image containing high-severity vulnerabilities from being deployed.
- Automated Compliance Auditing: Implementing audit logging policies that track every administrative action and alert security teams to unauthorized configuration changes.
- Runtime Threat Detection: Configuring tools like Falco to identify when a shell is opened inside a production container or when a sensitive file is accessed unexpectedly.
Your CKS Preparation Plan
14-Day Sprint (Accelerated)
This path is for those who live in the terminal every day and have a very fresh CKA. You should focus 70% of your time on the “Security-only” domains like Seccomp, AppArmor, and runtime security tools. Spend the final two days doing back-to-back mock exams to ensure your YAML editing speed is fast enough to beat the clock.
30-Day Steady Path (Recommended)
This is the most balanced approach for working professionals, allowing for 2 hours of study per day. Use the first two weeks to master the six core domains through documentation and short labs. Use the final two weeks for “muscle memory” practice, repeating complex tasks like configuring OPA and Admission Controllers until they become second nature.
60-Day Deep Dive (Comprehensive)
If you are coming from a traditional security background or haven’t touched K8s internals recently, this path is best. Spend the first month understanding the “Why” behind Linux kernel security and how it maps to container isolation. Use the second month for relentless hands-on practice, focusing on troubleshooting misconfigured security policies that break application functionality.
Common Mistakes to Avoid
- Treating it like a CKA Retake: Many candidates focus on administration and forget the security specifics. If you can’t manually edit a Kube-APIserver manifest to enable auditing, you will struggle.
- Slow Navigation of Documentation: The exam allows access to official docs, but if you spend 10 minutes searching for a policy template, you will run out of time. Practice finding specific security snippets in seconds.
- Ignoring the Host OS: Remember that Kubernetes runs on Linux. Forgetting to check file permissions on the underlying node or ignoring AppArmor profiles is a guaranteed way to lose points.
- Skipping Runtime Tools: Tools like Falco and Trivy are central to the CKS. Don’t just read about them; you must know their CLI flags and how to interpret their output.
Choose Your Path: 6 Specialized Learning Tracks
- DevOps Path: Focus on integrating security into the automation lifecycle. Your goal is to ensure that “security as code” is part of every Terraform script and Jenkins pipeline you write.
- DevSecOps Path: This is the ultimate destination for this certification. You will focus on “Shifting Left,” ensuring that security is a collaborative effort between developers and operations from the first line of code.
- SRE Path: Focus on the intersection of security and reliability. You will learn to build systems that aren’t just secure, but also resilient enough to stay online during a Distributed Denial of Service (DDoS) attack.
- AIOps/MLOps Path: Secure the massive data pipelines used for model training. This track ensures that your GPU-heavy nodes are not hijacked for unauthorized mining and that your training data remains private.
- DataOps Path: Focus heavily on data sovereignty and encryption. You will use CKS skills to manage secrets, encrypt data-at-rest in volumes, and ensure compliance with global data laws.
- FinOps Path: Security is a cost-saver. By mastering CKS, you can prevent “bill shock” caused by compromised clusters being used for unauthorized resource consumption or crypto-jacking.
Role → Recommended Certifications Mapping
| Role | Recommended Sequence | Why this path? |
| DevOps Engineer | CKA → CKS → Terraform | To automate infrastructure with a security-first mindset. |
| SRE | CKA → CKS → Prometheus | To maintain high uptime while ensuring the cluster is defended. |
| Security Engineer | CKS → CISSP → CCSP | To transition from traditional security into the cloud-native era. |
| Platform Engineer | CKA → CKS → KCSP | To build secure internal developer platforms (IDPs). |
| Cloud Engineer | Cloud Cert → CKA → CKS | To prove mastery of the underlying platform and the K8s layer. |
| Data Engineer | CKA → CKS → Data Certs | To ensure data pipelines are running on hardened infrastructure. |
| Engineering Manager | KCNA → CKA → CKS | To understand the technical debt and risks your team faces daily. |
Next Steps After CKS
- Same Track: Specialize in specific service mesh security (e.g., Istio) to manage complex microservice communications.
- Cross-Track: Move into Cloud Provider Security (like the AWS Certified Security Specialty) to secure the cloud environment outside of Kubernetes.
- Leadership: Pursue the Certified Information Systems Security Professional (CISSP) to move into strategic roles like CISO or Security Director.
Top Institutions for Training & Certification
- DevOpsSchool: This institution offers high-impact, expert-led training specifically designed for the CKS exam. Their curriculum focuses on live labs and real-world security scenarios, ensuring that students gain practical skills rather than just theoretical knowledge. They are widely recognized for their deep industry connections and post-training support.
- Cotocus: Known for their boutique, high-touch training approach, Cotocus provides intensive deep-dives into cloud-native security architecture. Their instructors are often active consultants who bring current production-level challenges into the classroom. It is an excellent choice for those who want to understand the “business logic” behind security decisions.
- Scmgalaxy: A massive repository of community-driven knowledge, Scmgalaxy offers extensive blogs, tutorials, and video content for DevOps professionals. They provide a wealth of free and paid resources that are essential for self-paced learners who want to master the broader DevOps ecosystem. Their community forums are a great place to troubleshoot complex K8s issues.
- BestDevOps: This school focuses on high-quality, practical training modules aimed at helping professionals clear their certifications on the first attempt. Their CKS program is streamlined to focus on the most-tested exam objectives, making it a very efficient choice for busy engineers. They emphasize speed and precision in the terminal.
- Niche Schools: Platforms like devsecopsschool.com, sreschool.com, aiopsschool.com, dataopsschool.com, and finopsschool.com offer hyper-specialized tracks. These are ideal for professionals who want to apply their CKS knowledge specifically within the domains of site reliability, artificial intelligence, or financial operations.
Frequently Asked Questions (FAQs)
1. How difficult is the CKS compared to the CKA or CKAD? The CKS is widely considered the most challenging of the three. While the CKA focuses on cluster administration and the CKAD on application deployment, the CKS requires a deep understanding of security vulnerabilities and the ability to harden a cluster using both native Kubernetes features and third-party security tools. It demands higher precision and faster execution under tight time constraints.
2. What are the mandatory prerequisites for taking the CKS exam? You must have a valid, non-expired Certified Kubernetes Administrator (CKA) certification to sit for the CKS. This is a hard requirement because the CKS builds directly on the administration skills—such as networking, troubleshooting, and cluster setup—that are validated in the CKA.
3. How much time should I realistically dedicate to preparation? For an engineer already comfortable with Kubernetes, a minimum of 4 to 6 weeks of dedicated study is recommended. This includes roughly 10–15 hours per week of hands-on lab practice. If you are less familiar with Linux security modules (like Seccomp or AppArmor), you may need an additional 2–3 weeks to master those host-level concepts.
4. In what sequence should I take the Kubernetes certifications? The most logical and effective path is KCNA → CKA → CKS. The KCNA provides the conceptual overview, the CKA gives you the administrative “muscle memory,” and the CKS adds the specialized security layer. Attempting the CKS without mastering the CKA fundamentals often leads to frustration during the performance-based tasks.
5. What is the value of the CKS in the current job market? As organizations move more sensitive workloads to the cloud, security has become a board-level priority. The CKS is one of the few certifications that proves you can actually do the work of securing a cluster, not just talk about it. It acts as a major differentiator, often placing candidates in a higher salary bracket and making them eligible for “Security Architect” or “Lead DevSecOps” roles.
6. What are the primary career outcomes after earning a CKS? Holding a CKS opens doors to specialized roles such as DevSecOps Engineer, Cloud Security Architect, and Senior SRE. It also positions you as a technical lead who can bridge the gap between pure security teams and pure engineering teams, making you indispensable during infrastructure audits and architectural reviews.
7. Does the CKS help with salary growth? Yes, significantly. In both the Indian and global markets, security-certified professionals often command 20% to 35% higher salaries than their non-certified counterparts. Because there is a massive talent gap in cloud-native security, companies are willing to pay a premium for verified experts who can prevent multi-million dollar data breaches.
8. Is the exam multiple-choice or performance-based? It is 100% performance-based. You will not find any multiple-choice questions. You are given a set of real-world scenarios in a terminal environment and must execute commands, edit YAML files, and configure policies to secure the cluster within a 2-hour window.
9. How long is the CKS certification valid? The certification is valid for 2 years. Because the Kubernetes ecosystem and security threats evolve so rapidly, the CNCF requires recertification to ensure your skills remain relevant to the current versions of Kubernetes and the associated security tooling.
10. Can I take the CKS if my CKA has expired? No. You must have an active CKA certification at the time you take the CKS exam. If your CKA has expired, you will need to retake and pass the CKA before you are eligible to attempt the CKS.
11. Is the CKS worth it for a Manager or Lead who doesn’t code daily? While the exam is very technical, the process of preparing for it is invaluable for leadership. It provides a deep understanding of the risks inherent in containerized environments, allowing managers to better estimate project timelines, select the right security vendors, and build more resilient engineering cultures.
12. What happens if I fail the exam on my first attempt? Most exam vouchers purchased through the Linux Foundation or authorized partners include one free retake. This is a great safety net, as it allows you to experience the actual exam environment and time pressure, identify your weak points, and return stronger for the second attempt.
CKS Specific FAQs
1. What is the primary focus of the CKS exam?
The exam focuses on the “Four Cs” of Cloud Native Security: Cloud, Cluster, Container, and Code. You will be tested on how to secure each layer effectively.
2. How do I practice for the runtime security section?
The best way is to set up a local lab using Minikube and install Falco. Practice creating custom rules that detect when someone tries to modify a sensitive file like /etc/shadow.
3. Are there many questions on third-party tools?
Yes, you should be very comfortable with tools like Trivy for scanning images, Kube-bench for checking CIS compliance, and Falco for runtime alerts.
4. How important is “Supply Chain Security”?
It is critical. You must know how to audit a Dockerfile for security best practices and how to use Admission Controllers to prevent insecure images from ever being scheduled.
5. Do I need to be a Linux expert?
You don’t need to be a kernel developer, but you should be very comfortable with the Linux command line, file permissions, and basic networking concepts like IPTables.
6. Is the CKS exam updated frequently?
Yes, the CNCF updates the exam to match the current minor version of Kubernetes. Always ensure your study materials match the version of Kubernetes currently being used in the exam.
7. Is RBAC heavily tested?
Role-Based Access Control (RBAC) is the heart of Kubernetes security. You should expect to see RBAC integrated into almost every question on the exam.
8. Can a non-technical Manager benefit from CKS knowledge?
While they may not take the exam, understanding the CKS domains allows a manager to make informed decisions about security budgets, tool selection, and hiring priorities.
Testimonials
“Earning my CKS was the turning point in my career. It moved me from being ‘the guy who fixes the cluster’ to ‘the architect who secures the business.’ The training from DevOpsSchool provided the exact hands-on rigor I needed to pass on my first try.”
— Ananya R., Senior DevSecOps Engineer
“The CKS exam is the most challenging thing I’ve done in a decade of tech. It’s not about memorizing; it’s about doing. This certification proved to my clients that I can handle the most sensitive cloud-native workloads with confidence.”
— Marcus T., Platform Security Architect
Conclusion
Securing a Kubernetes cluster is an ongoing battle, not a one-time setup. The Certified Kubernetes Security Specialist (CKS) certification provides you with the tactical skills and strategic mindset needed to defend modern infrastructure against evolving threats. In a world where a single misconfiguration can lead to a massive data breach, being a certified security expert is the ultimate professional advantage.